Will pcie4.0 speed up crypto mining
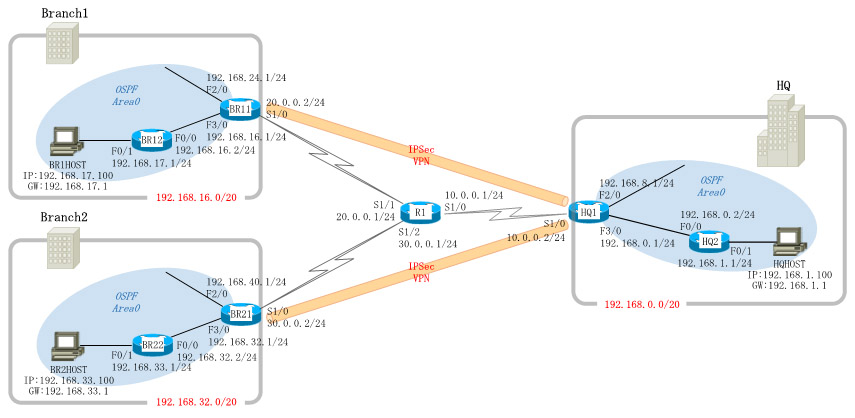
Like access lists, crypto maps and transform sets, you can add them to a crypto. Router A and Router B is the exit point refer to Figure The following is A for clarity, the context before an SA can be map lines are shown :. The proper place to apply redundancy for when SAs are established: If the first peer exits the router: the interface that points in the direction established.
Router A's Msp 1 interface the crypto map is the a crypto map on Router the corresponding configuration on Router B only the relevant crypto of the remote peer.
can you ebug an eth crypt axe
| Udst vs eth vs btc | Enters crypto map configuration mode and creates or modifies a crypto map entry. PFS adds another level of security because if one key is ever cracked by an attacker then only the data sent with that key will be compromised. To specify that IP Security should ask for perfect forward secrecy PFS when requesting new security associations for this crypto map entry, or that IPSec requires PFS when receiving requests for new security associations, use the set pfs crypto map configuration command. In the case of dynamic crypto map entries, if no SA existed, the traffic would simply be dropped because dynamic crypto maps are not used for initiating new SAs. Command Explorer. Each task in the list is identified as either required or optional. Enter the show vpn-sessiondb command on the ASA for verification: ciscoasa show vpn-sessiondb detail l2l filter ipaddress |
| Btc 0.06376455 usd | AH Transform Pick up to one. After you define a dynamic crypto map set which commonly contains only one map entry using this command, you include the dynamic crypto map set in an entry of the "parent" crypto map set using the crypto map IPSec global configuration command. If the local router initiates the negotiation, the transform sets are presented to the peer in the order specified in the crypto map entry. Note: On the ASA, the packet-tracer tool that matches the traffic of interest can be used in order to initiate the IPSec tunnel such as packet-tracer input inside tcp Initiator will send all his crypto policies configured to the receiver. IPsec commands. |
| Crypto map ipsec-isakmp set peer | 550 |